Six Things to Know About Industrial Robot Cyber Security
Recently, Elon Musk and dozens of other technocrats stoked public fears about "killer robots" by petitioning the United Nations to ban autonomous technology being used in (or as) weapons.
"We should not lose sight of the fact that, unlike other potential manifestations of AI which still remain in the realm of science fiction, autonomous weapons systems are on the cusp of development right now and have a very real potential to cause significant harm to innocent people along with global instability," said Ryan Gariepy, founder of Clearpath Robotics, in a statement.
But with all the focus on machine-gun toting cyborgs, are Musk and others overlooking the dangers of industrial and consumer robots?
That's a question being taken up by the lead researchers at Seattle-based cybersecurity firm IOActive, Cesar Cerrudo and Lucas Apa. In their recent paper, "Hacking Robots Before Skynet," the team warns of the impending vulnerabilities popular robots have to hackers and the potential threat they pose.
"Industrial robots are more widely adopted and are the most dangerous since they work side-by-side with people, so there is a genuine and important danger there," the researchers responded via email. "The threats are real and possibilities are out there. It's just matter of someone deciding to exploit them."
To demonstrate the threat, the team released a video showing how a UBTech Alpha 2 robot can be hacked through an unprotected USB port to attack a tomato with a screwdriver.
While this example won't worry Musk and his compatriots, the authors say this type of attack could someday jump to much bigger, stronger industrial robots.
"This new generation works hand-in-hand with humans, assisting them, rather than just performing automated operations," the researchers say. "That's why we believe these robots need to be secured first, since they currently work very close to workers and they are also powerful. We found it was possible to disable human safety protections by hacking the robot remotely and also move its arms to cause harm. This is an attack that could be used to directly threaten human life."
The team found 50 vulnerabilities in their investigation with the robots' core components that "bring them to life," although tests with fully operational industrial robots themselves were not done. Each vendor was made aware of these issues and technical details will be made available later in the year.
Rethink Robotics says vulnerabilities to its Baxter and Sawyer robots have been addressed and patched through its Intera 5 software, and that two specific weaknesses are intentional for the research and educational versions. Universal Robots told us they are constantly monitoring for threats and are aware of IOActive's findings, but couldn't go into details. On the consumer side, UBTech told Forbes IOActive's tomato-stabbing video was "sensationalistic" and "an exaggerated depiction of Alpha 2's open-source platform."
In fairness, sensationalism sells, and oftentimes it takes an extreme example to get people to pay attention to the real, less murderous dangers.
Because, sure, a computer savvy sadist or terrorist taking over a collaborative robot is certainly a scary thought, and it does have the potential for a trashy Halloween season slasher flick. But someone hijacking a robot's cameras in your plant or home, or intercepting your network info, is enough cause for concern.
That doesn't mean you should constantly fear your warehouse AGV is going to go "Christie" on you, or that Pepper the robot will throttle you in your sleep. It does mean you should consider security as seriously as you do cost and productivity gains when deciding on a new robot.
Here are five areas to look at:
1. Check the Specs
When shopping for any piece of equipment, you make sure it fits the needs of your application. Does it have the right speed, strength, durability, etc.? Cyber security specifications should have equal consideration to operational and environmental requirements. And if the manufacturer doesn't make these easy to find, move on.
"Plants should check for security features before buying a robot," Cerrudo and Apa say. "If the robot has few or no security features in their marketing material, then that's not a good indication."
2. Secure Communications:
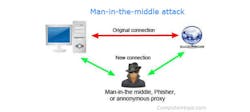
IOActive found that UBTech's Alpha 1S was left open for a "man-in-the-middle" attack, meaning a third party could sneak malware in while the robot is receiving updates or commands from a device or app. This was because the app allegedly did not use cryptographically strong communication. The easiest way to prevent this is to always make that communication to any end point connected to your robot is encrypted.
3. Network Isolation
This is just common sense. You wouldn't access your company records from a coffee shop WiFi without a VPN, and you shouldn't talk to your robot over an unsecure network.
"While it's very important to keep industrial robots on isolated networks, attacks and vulnerabilities will remain if the products are vulnerable or not patched," IOActive advises.
4. Authenticate
Always require authentication, meaning at the very least a username and password. This prevents a disgruntled employee or saboteur from sending harmful commands to a robot via Bluetooth from the parking lot and shutting down your production line.
"This is one of the most critical problems we found, allowing anyone to remotely and easily hack the robots," the authors say.
5. Component Isolation:
"Typically all the components are not isolated from each other, which means that if you can hack one of the services, you can compromise the entire operating system," Cerrudo and Apa explain. "This means that any software-based human safety protection can always be disabled if any service from the robot gets hacked. That's why human safety protections should be isolated as much as possible from the other components that are usually more exposed."
Here's a video of what happens a six-axis arm's paramters being changed:
6. Segmentation
If you recall the Target breach, a contractor's laptop got hacked and the malware made its way onto the retailer's VPN and had a clear path to the point-of-sale terminals, and thousands of credit card numbers. There's no good reason a vendor's credentials should allow access to a major corporation's most valuable data or resources, and the same holds true for a factory and its robots and other major equipment.
Policy-based security solutions, such as Bayshore IT/OT Gateway, put up extra barriers and conducts deep inspections of industrial traffic for attacks, allowing only users verified by multiple sources to access your key equipment. Bayshore says their cloud-based solution can even prevent StuxNet, the worm that brought down Iran's uranium enrichment facility a decade ago.
About the Author
John Hitch
Editor, Fleet Maintenance
John Hitch, based out of Cleveland, Ohio, is the editor of Fleet Maintenance, a B2B magazine that addresses the service needs for all commercial vehicle makes and models (Classes 1-8), ranging from shop management strategies to the latest tools to enhance uptime.
He previously wrote about equipment and fleet operations and management for FleetOwner, and prior to that, manufacturing and advanced technology for IndustryWeek and New Equipment Digest. He is an award-winning journalist and former sonar technician aboard a nuclear-powered submarine where he served honorably aboard the fast-attack submarine USS Oklahoma City (SSN-723).